Open-Source CVE Triage: Combining NVD, CISA KEV, and EPSS in One MCP Server
Your vulnerability scanner dumps 200 CVEs. You sort by CVSS score. The CVSS 9.8 at the top gets your attention. You patch it first.
Meanwhile, a CVSS 5.0 three pages down is in active ransomware campaigns. CISA added it to the Known Exploited Vulnerabilities catalog last week. EPSS gives it an 80% exploitation probability. Nobody looked at it because it was page three.
CVSS tells you how bad a vulnerability could be. It says nothing about whether anyone is actually exploiting it. For that, you need two more data sources — and nobody combines all three in one place.
Until now. vulnerability-intelligence-mcp is an open-source MCP server that pulls from NIST NVD, CISA KEV, and FIRST.org EPSS, computes a composite risk score, and gives your AI 30 tools for CVE analysis, watchlist tracking, and scanner triage.
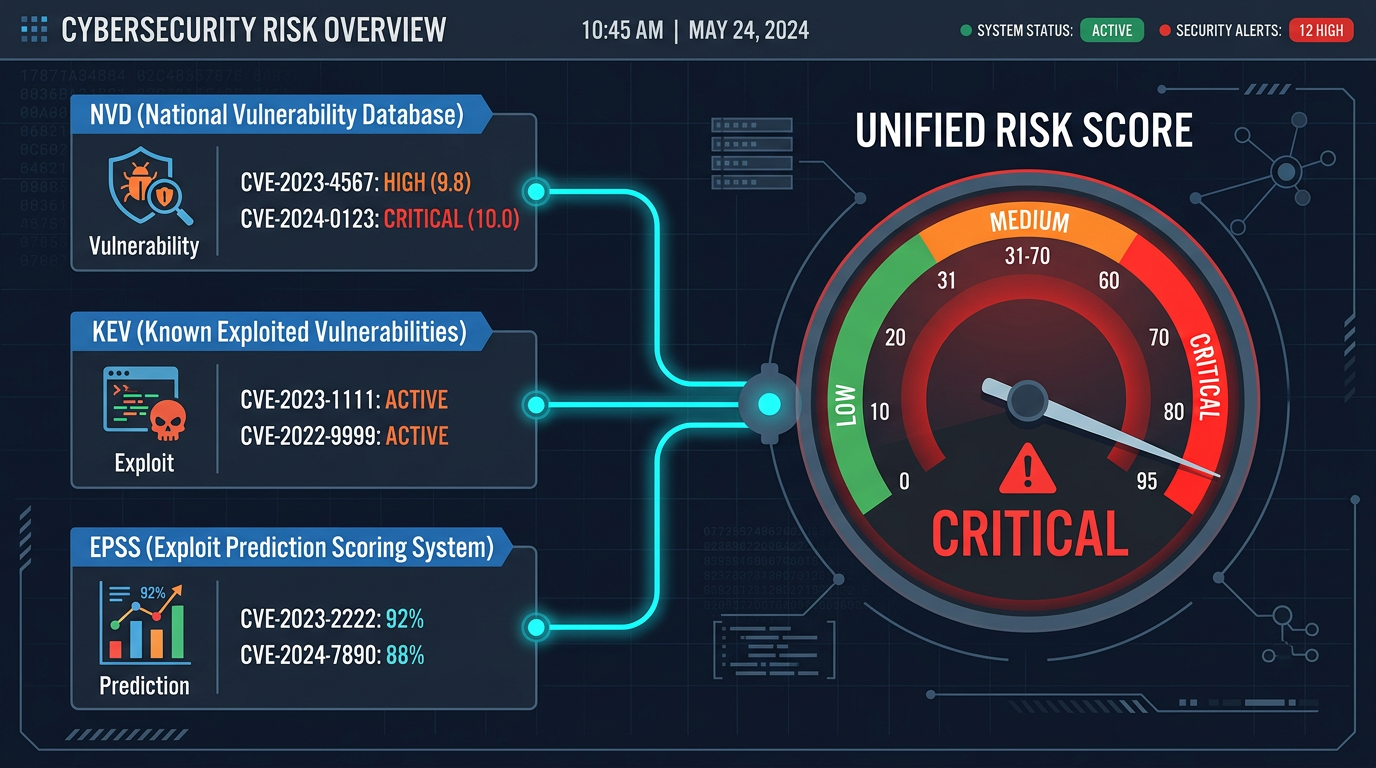
The three data sources
NIST NVD (National Vulnerability Database) is the canonical CVE registry. It tells you what a vulnerability is — the affected products, the CVSS severity score, the weakness type (CWE), and when it was published. This is the "how bad could it be" signal.
CISA KEV (Known Exploited Vulnerabilities catalog) is ground truth for active exploitation. If a CVE is in the KEV catalog, CISA has confirmed that threat actors are exploiting it right now. Not theoretically — actively. The catalog also flags which CVEs are linked to ransomware campaigns.
FIRST.org EPSS (Exploit Prediction Scoring System) is a machine learning model that predicts the probability of a CVE being exploited in the next 30 days. It's trained on real exploitation data and updated daily. An EPSS score of 0.85 means there's an 85% chance this CVE will be exploited in the wild within a month.
Each source answers a different question:
| Source | Question | Update frequency |
|---|---|---|
| NVD | How severe is this vulnerability? | As CVEs are published |
| KEV | Is it being exploited right now? | As exploitation is confirmed |
| EPSS | Will it be exploited soon? | Daily |
Individually, each is useful. Combined, they tell you exactly what to patch first.
The scoring algorithm
The composite score combines all three sources into a single 0–10 number with a risk tier (CRITICAL, HIGH, MEDIUM, LOW):
base = cvss_base_score if available else 5.0
epss_multiplier = 1.0 + (epss_score * 2.0)
composite = base * epss_multiplier
if in_cisa_kev:
composite += 2.0
if ransomware_linked:
composite += 1.0
composite = clamp(composite, 0.0, 10.0)
The logic: start with the CVSS base score, then amplify it by exploitation probability. A high EPSS score can double the effective severity. Active exploitation (KEV) adds a flat +2.0 bonus. Ransomware linkage adds another +1.0. The result is clamped to 10.
Tier thresholds: CRITICAL ≥ 9, HIGH ≥ 7, MEDIUM ≥ 4, LOW < 4.
Any source can be missing — the score degrades gracefully. If NVD has no CVSS data, it assumes 5.0. If EPSS has no score, the multiplier stays at 1.0. If KEV lookup fails, no bonus is added. You always get a usable score.
Why this reranks your scanner output
Consider two CVEs in the same Trivy scan:
CVE-A: CVSS 5.0, EPSS 80%, in CISA KEV, ransomware-linked
5.0 × (1 + 0.8 × 2) + 2.0 + 1.0 = 5.0 × 2.6 + 3.0 = 16.0→ clamped to 10.0 — CRITICAL
CVE-B: CVSS 7.5, EPSS 0.3%, not in KEV
7.5 × (1 + 0.003 × 2) = 7.5 × 1.006 = 7.55→ HIGH
Your scanner ranked CVE-B higher because CVSS 7.5 > 5.0. The composite score flips the priority: CVE-A is the one in active ransomware campaigns. CVE-B is a theoretical risk nobody is exploiting.
Run it yourself
git clone https://github.com/thinkchainai/vulnerability-intelligence-mcp
cd vulnerability-intelligence-mcp
pip install .
NIST_NVD_API_KEY=your_key vulnerability-intelligence-mcp
CISA KEV and EPSS are public APIs — no additional keys needed. Get a free NVD API key at nvd.nist.gov (takes 30 seconds).
Without a key, NVD requests are rate-limited to 5 per 30 seconds. With a key: 50 per 30 seconds.
30 tools across five categories
| Category | Tools | What they do |
|---|---|---|
| Combined | vulnerability_app, vulnerability_analyze | Interactive dashboard and full cross-source CVE analysis |
| NVD | 8 tools | CVE lookup, search, severity filtering, CPE matching, history, weakness breakdown |
| CISA KEV | 9 tools | Catalog stats, recent additions, ransomware-linked CVEs, remediation deadlines, product exposure |
| EPSS | 8 tools | Score lookup, most exploitable, score history, percentile filtering, risk reports |
| Profile | manage_stack, manage_watchlist, scan_triage | Your tech stack, CVE watchlist with delta tracking, scanner output triage |
The profile tools make repeated use genuinely useful:
Technology stack profiling — tell the server what you run (nginx 1.24, postgresql 16, ubuntu 22.04). Every subsequent CVE lookup automatically flags whether the vulnerability affects your stack.
CVE watchlist — track specific CVEs over time. The server captures baseline EPSS and KEV status when you add a CVE, then reports deltas on every check. You'll know when a watched CVE's exploitation probability spikes or when it gets added to the KEV catalog.
Scanner triage — paste raw Trivy JSON, Grype JSON, CSV, or any text containing CVE IDs. The server extracts every CVE, scores them across all three sources in parallel, cross-references your technology stack, and returns a prioritized triage report grouped by risk tier.
Example: triage a Trivy scan
Run Trivy against your container image, then hand the output to your AI:
"Triage this scan output: [paste Trivy JSON]"
The scan_triage tool extracts all CVE IDs, queries NVD + KEV + EPSS for each in parallel, and returns:
{
"total_cves": 47,
"by_tier": {
"critical": 3,
"high": 8,
"medium": 22,
"low": 14
},
"stack_affected": 2,
"results": [
{
"cve_id": "CVE-2024-6387",
"composite_score": 10.0,
"risk_tier": "CRITICAL",
"rationale": "CVSS base 8.1; EPSS 91.5%; confirmed actively exploited (CISA KEV)",
"in_your_stack": true,
"affected_technologies": ["openssh"]
}
]
}
47 CVEs from your scanner, instantly triaged into 3 you need to act on today, 8 you should plan for this sprint, and 36 that can wait.
Architecture
The server is a standard MCP server built with FastMCP. Three async API clients handle the data sources:
NVDClient— authenticated requests to the NVD 2.0 APICISAKEVClient— fetches the KEV catalog (public, no auth)EPSSClient— queries the FIRST.org EPSS API (public, no auth)
Profile data (tech stack, watchlist, briefing state) persists to a local SQLite database at ~/.vulnerability-intelligence/state.db. This directory is outside the package installation path, so pip install --upgrade preserves your data.
Use it without installing anything
If you don't want to run the server locally, the same 30 tools are available as a hosted bundle at mcpbundles.com/bundle/vulnerability-intelligence. One URL, works with Claude, ChatGPT, Cursor, or any MCP client.
Source
MIT licensed. PRs welcome.
GitHub: github.com/thinkchainai/vulnerability-intelligence-mcp